Note: The following features are not added to IT Risk Management by default. For information on adding these features to your version of the app, contact your CSM.
New Features
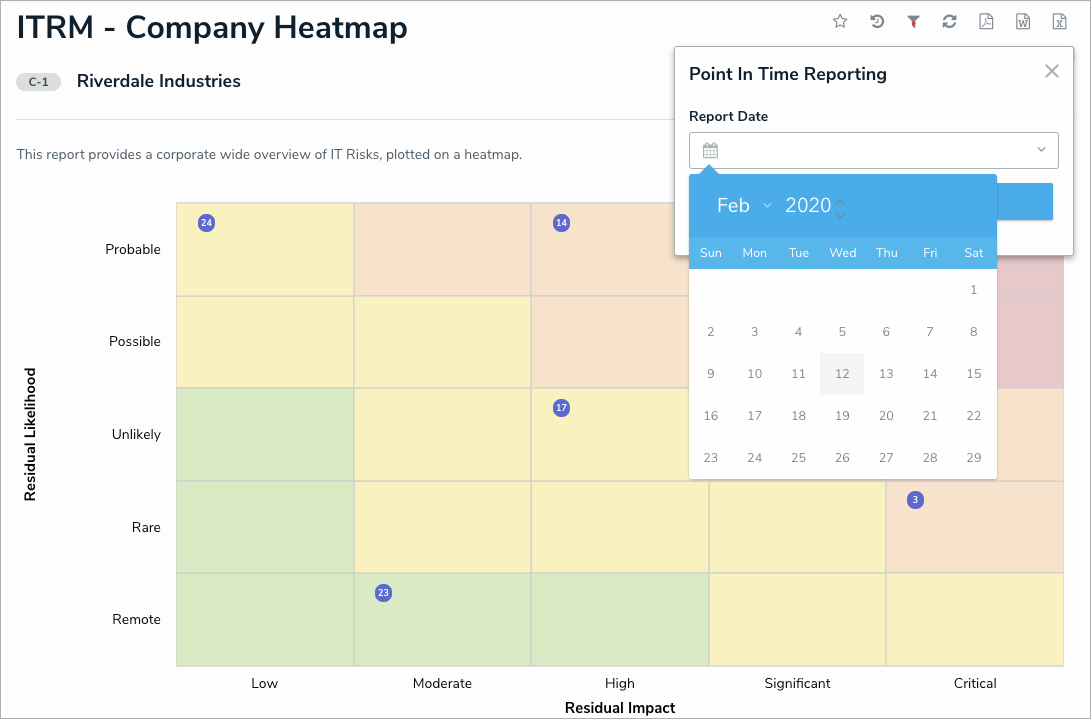
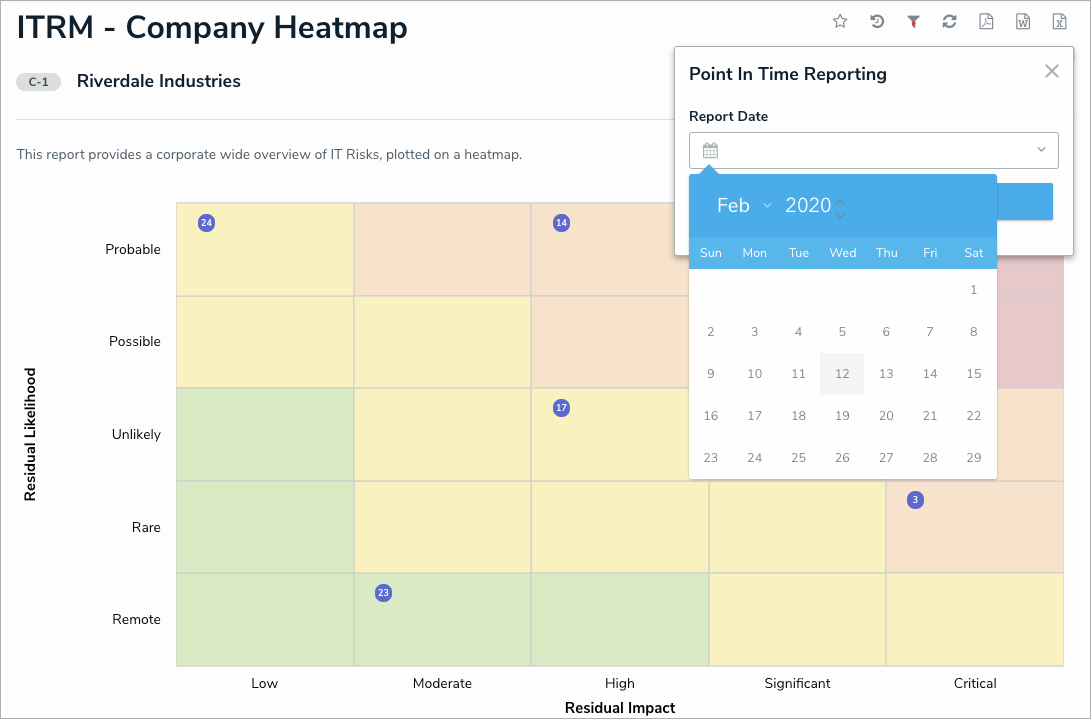
Point in Time Reporting
With the new Point-in-Time reporting feature, users can view historical information in reports in order to compare and contrast against previous risk assessments. For instance, an IT risk team can easily compare issue overview reports across several months to easily identify trends and demonstrate progress. Admins can enable this feature from the Configure Filters palette when editing a report.
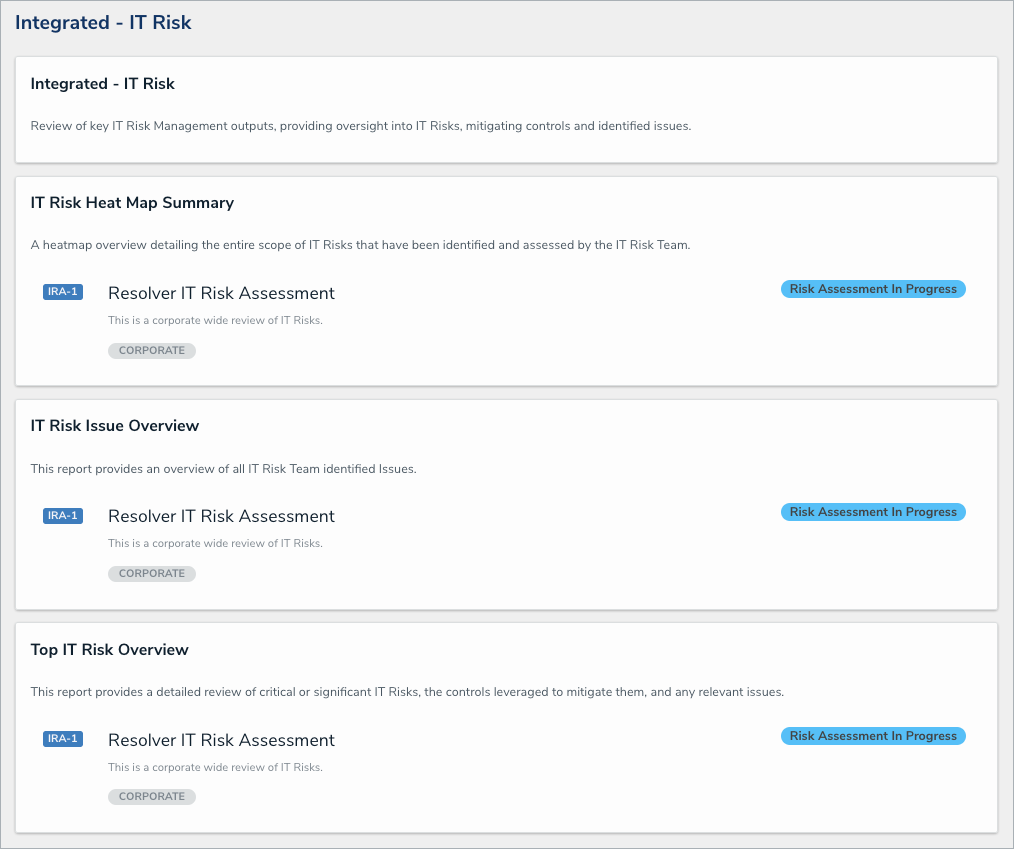
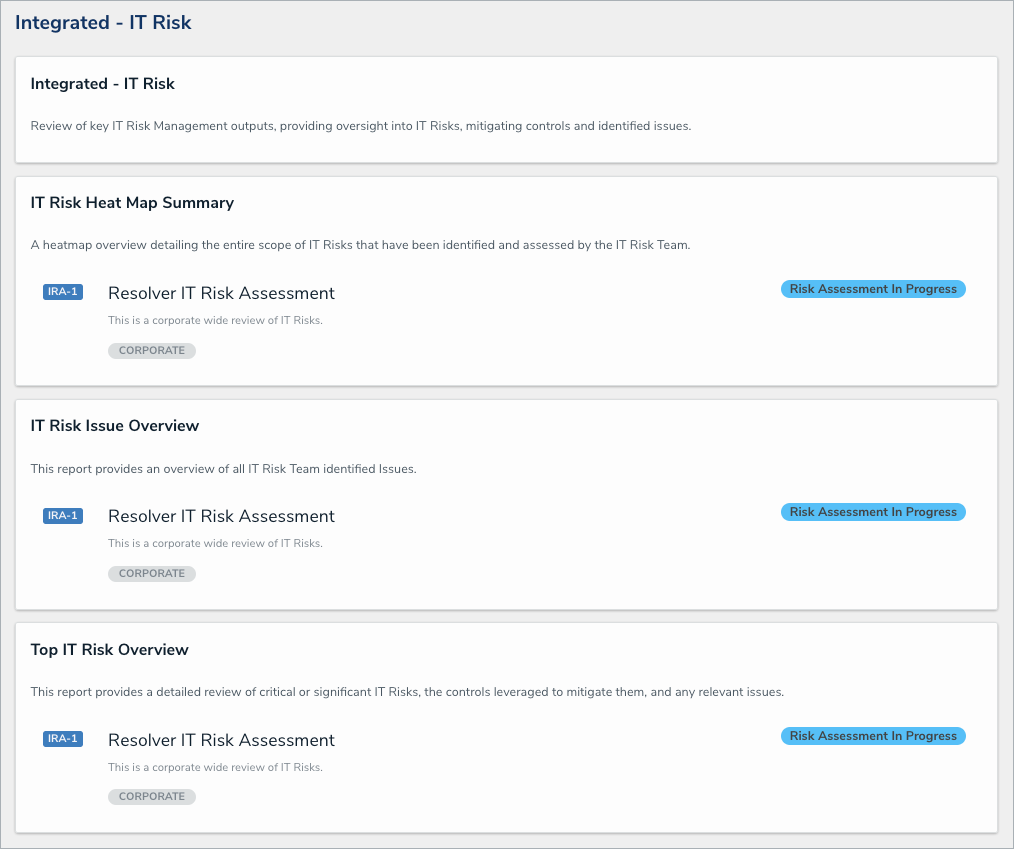
Risk Management Integration
Users in the Risk Management app's Risk Team user group can now leverage their Integrated — IT Risk report to review key risks, controls, and issues from IT risk assessments. This will help to automate direct reporting for the IT risk team and ensure the risk team has the most up-to-date information.
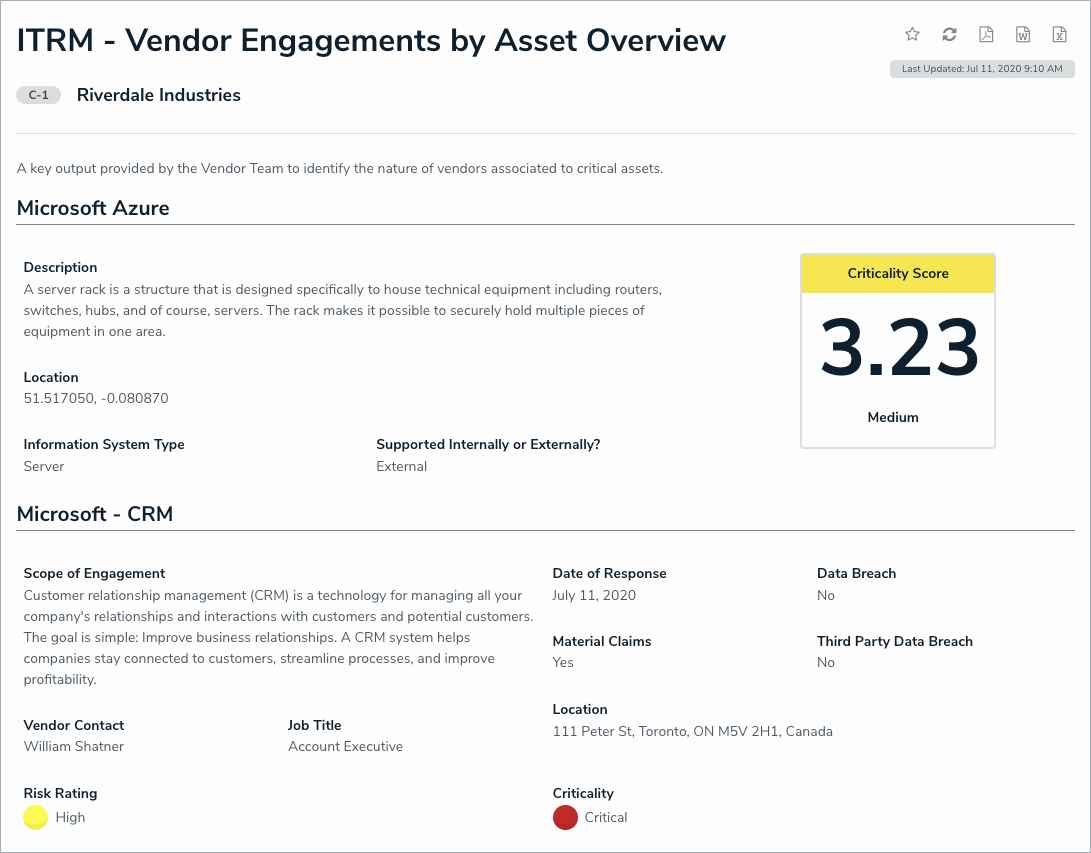
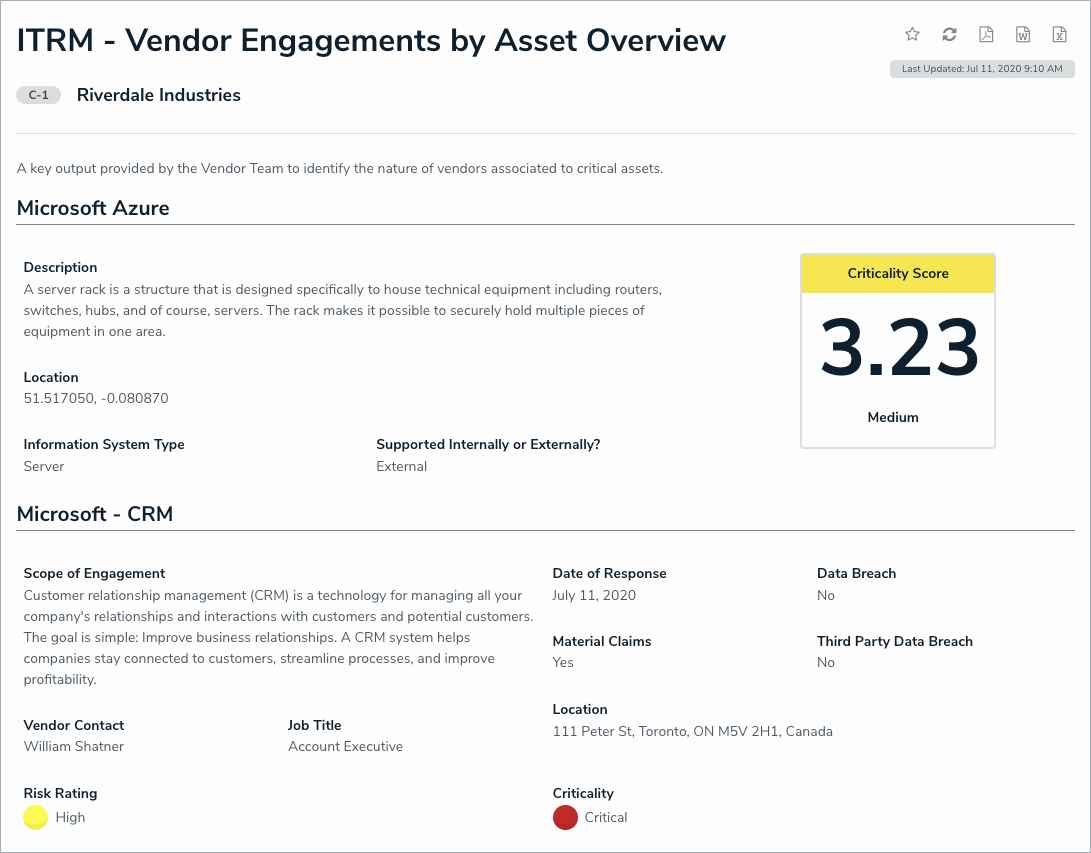
Vendor Risk Management Integration
Users in the IT Risk Team user group can view vendor information that has been linked to an asset by a member of the Vendor Team user group from the Vendor Risk Management app. This will increase visibility between the two apps, provide IT risk teams with more detailed information about the vendors that support their assets, and strengthen their decision making abilities.
These links can be viewed in greater detail in the new Vendor Engagements by Asset Overview report.
Archive Support
Members of the IT Risk Administrator user group can now access the new Archived activity to view the following archived objects:
Assessments
IT Risks
Controls
Issues
The Library will have new views to allow users to view the following archived objects:
Information Assets
Threats
Vulnerabilities
IT Risk Register
Assessment Scoping Improvements
The IT Risk Assessment form has been enhanced to better support scoping exercises. When the IT risk team is scoping an assessment, instructions will be visible to walk them through the process. After scoping, the instructions will be replaced with a tabular view of the scope for simple reference. This will reduce confusion on users and make the scoping process easier overall.
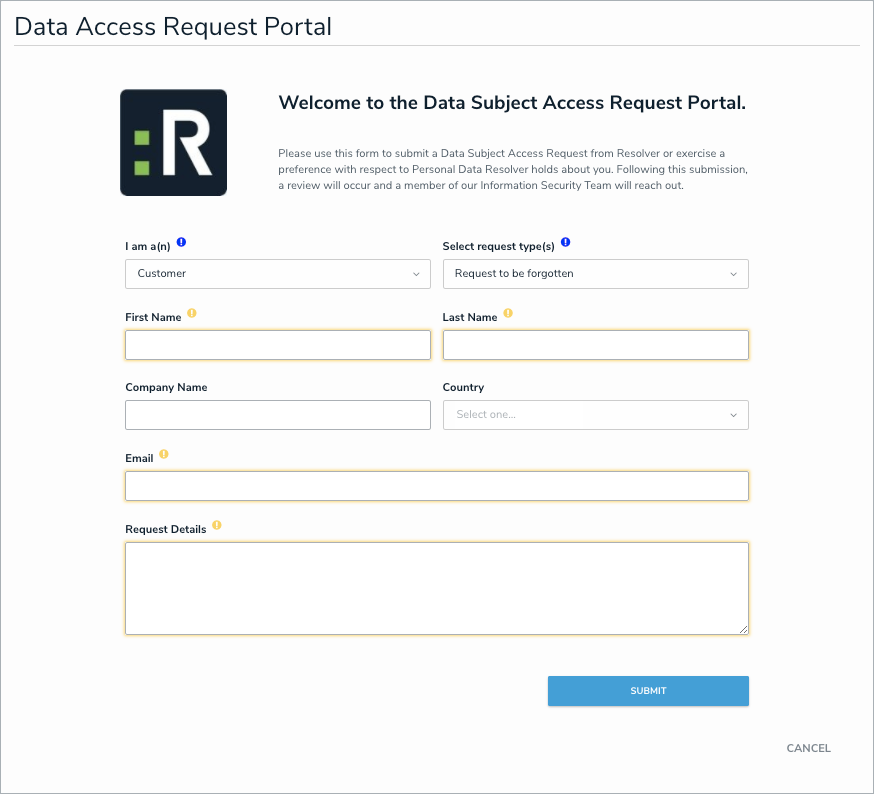
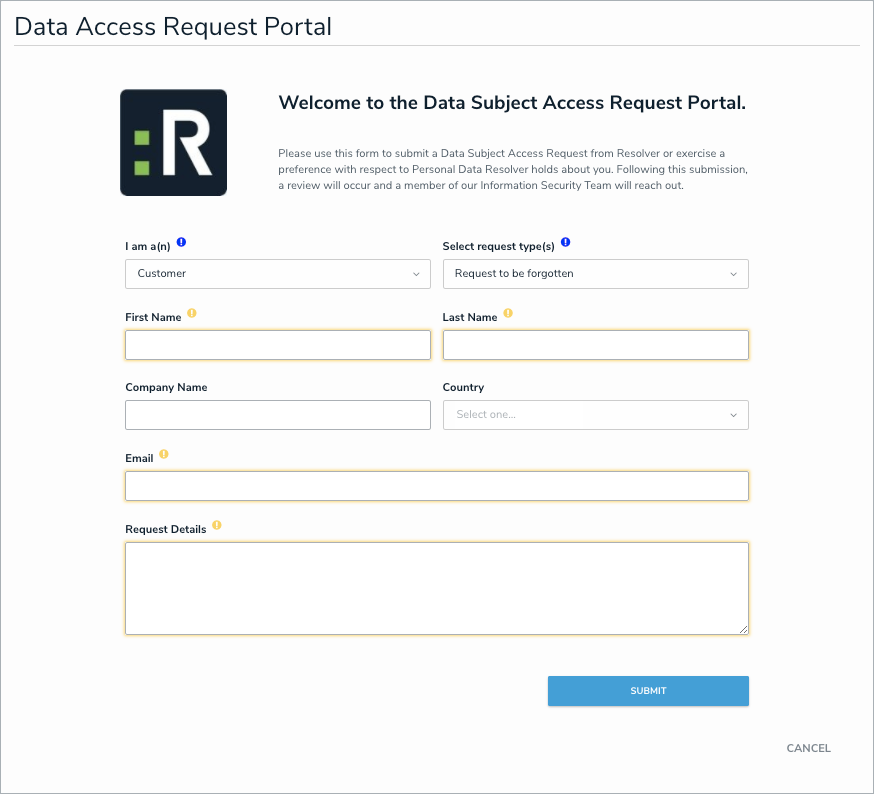
Data Subject Access Request Portal
Users in the IT Risk Team user group can use the new Data Subject Access Request Portal activity to collect important requests regarding personal identifiable information. These requests can then be verified by the InfoSec team and tracked to completion, taking an important responsibility and centralizing that effort into a single monitoring activity.
Miscellaneous Improvements
When a risk moves from the Monitoring stage to either the Review or Assessment stage, the Last Assessed Date field will be set to the current date. This will be visible on the following forms
IT Risk Review
IT Risk Monitoring
Top IT Risk Repeatable
Members of the Issue Owner user group will have read-only access to IT risk assessments in the following workflow states:
Assign IT Risk Owner & Profile
Assessment
Monitoring
Review